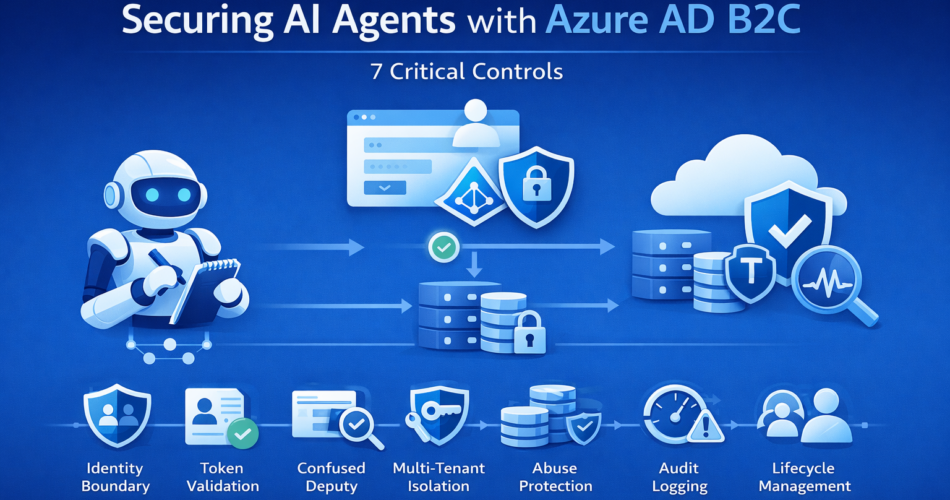
Securing AI agents with Azure AD B2C becomes essential once your system moves beyond internal testing and begins serving real users with real data. In early prototypes, agents often run behind a shared service key. Authentication is simplified. Authorization is implicit. Everything appears stable.
Then external users arrive.
Multiple tenants authenticate simultaneously. Tokens are reused incorrectly. An agent invokes downstream APIs without verifying user scope. A prompt attempts to retrieve data outside the authenticated context.
The system may not fail visibly, but trust boundaries begin to erode.
Identity in agent systems is not just about login screens. It defines who can ask questions, what the agent is allowed to access, and which actions are permitted on behalf of the user. Without explicit enforcement, reasoning logic becomes a security risk.
Before implementing identity controls, one question should be answered clearly.
When Azure AD B2C Is Necessary
Azure AD B2C is appropriate when:
- Agents serve external or consumer identities
- User-specific data influences responses
- Multi-tenant access is required
- Compliance demands traceable user identity
It may be unnecessary when:
- Agents operate only under internal service accounts
- User identity does not affect authorization decisions
Identity infrastructure adds operational complexity. It should address real authorization requirements — not exist simply for architectural completeness.
1. Separate User Identity from Agent Privilege
Two identities exist in an agent system:
- The authenticated user (via Azure AD B2C)
- The service identity the agent uses to access Azure resources
A secure request flow should look like this:
- User authenticates through Azure AD B2C
- Application validates the JWT token
- Claims are extracted (roles, tenant, scopes)
- Authorization is evaluated against user claims and policy rules
- The agent performs only permitted actions using managed service identity
The agent must not inherit unrestricted infrastructure privileges based solely on successful authentication.
Tradeoff:
Additional authorization logic and middleware complexity.
Advantage:
Enforces least privilege consistently and prevents privilege escalation.
2. Token Validation and Claims Enforcement
Every request must validate:
- Issuer
- Audience
- Signature
- Expiration
After validation, claims must be enforced explicitly:
decoded_token = validate_jwt(token)
if "risk_reader" not in decoded_token["roles"]:
raise UnauthorizedAccess()Authorization must occur before any tool invocation or data retrieval.
Tradeoff:
Increased request processing overhead.
Advantage:
Ensures that agent decisions align with defined access policies.
3. Preventing the Confused Deputy Problem
The “confused deputy” problem occurs when a privileged service performs actions on behalf of a user without verifying whether that user is authorized to perform them.
In an AI system:
- The agent has high-privilege access to infrastructure.
- A user prompt requests restricted data.
- The agent retrieves it because its service identity allows it.
The agent unintentionally misuses its authority.
Mitigation requires:
- Validating user claims
- Mapping claims to permitted operations
- Restricting downstream calls to authorized scope
Tradeoff:
Requires clear mapping between claims and permissible actions.
Advantage:
Prevents privilege escalation through reasoning logic.
4. Multi-Tenant Isolation
For multi-tenant systems, isolation must be enforced at the data layer.
Recommended controls:
- Include
tenant_idin partition keys - Validate tenant claim on every query
- Reject cross-tenant access attempts
Example:
if request_tenant_id != decoded_token["tenant_id"]:
raise UnauthorizedAccess()Tradeoff:
Increased schema and validation complexity.
Advantage:
Strong tenant isolation guarantees.
5. Abuse Protection: Rate Limits and Prompt Injection
Rate limiting protects against:
- Credential stuffing
- Automated scraping
- Token replay
However, rate limiting alone does not mitigate prompt injection.
Prompt injection is a logic-level attack where input attempts to override system instructions or escalate privileges. Identity enforcement reduces its impact by:
- Enforcing strict authorization checks
- Restricting tool access based on roles
- Preventing arbitrary downstream queries
A layered defense includes:
- Per-user rate limiting
- API Management throttling
- Claims-based authorization
- Tool-level permission enforcement
Tradeoff:
More operational configuration.
Advantage:
Reduced abuse surface across identity and reasoning layers.
6. Observability and Audit Logging
Track:
- Authentication failures
- Token validation errors
- Unauthorized action attempts
- Role mismatch events
Example:
logger.warning(
"authorization_failure",
extra={
"user_id": decoded_token["sub"],
"required_role": "risk_reader"
}
)Auditability enables compliance reporting, forensic investigation, and anomaly detection without manual reconstruction.
Tradeoff:
Increased logging volume.
Advantage:
Clear traceability of identity-related decisions.
7. Lifecycle and Revocation Management
Define policies for:
- Account deactivation
- Password resets
- Lockout thresholds
- Token revocation
Long-running workflows must not cache claims beyond token expiration. Revoked users should lose access immediately.
Tradeoff:
Operational overhead in identity lifecycle management.
Advantage:
Prevents stale authorization from persisting unnoticed.
Final Thoughts
Security in agent systems is not about adding authentication. It is about enforcing identity constraints at every decision boundary.
Azure AD B2C introduces:
- Claims enforcement responsibilities
- Tenant isolation requirements
- Abuse mitigation controls
- Audit and governance obligations
Implicit identity assumptions simplify early development but expose systems to privilege escalation and data leakage. Explicit validation, authorization checks, and observability increase engineering effort but enable safe production deployment.
Identity enforcement is architectural, not cosmetic.